Apple has always been a technology company that focuses on privacy. Its ecosystem can tend to feel safer than most of the alternatives, whether it is through encrypted messaging, strict app review policies, and many more. Such products as the iPhone, iPad, and MacBook are sold on security as a major promise. That promise is weighty to many users particularly those who are professionals dealing with financial information and personal management records. Yet no system is flawless. Threats to cyber and their dynamics are ever-changing. Hackers adapt quickly. Although Apple products are characterized by amazing protections, the physical security is manifested in updates of software, user activity, and new vulnerabilities. By knowing their advantages and disadvantages, a better perspective is provided on the precision of the security of these machines.
Closed Ecosystem Advantage

The ecosystem by Apple is highly restrained meaning that apps do not have free access to the system files. This architecture minimizes attacks on malicious software. This is a contrast to open platforms where apps are published into the App Store without Apple screening them first, and therefore provides an extra barrier of protection.
Hardware and Software Integration
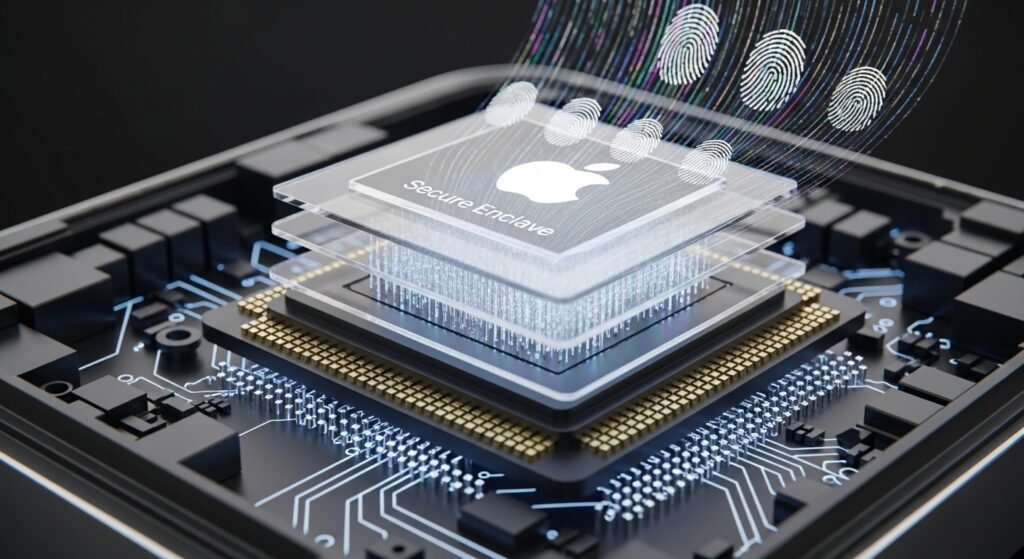
The Apple hardware and software design occur together. Such an integration enables such features as Secure Enclave to safeguard biometric information. The coordinated design also tends to minimize compatibility faults which attackers normally use on fragmented systems.
Regular Software Updates

New vulnerabilities are fixed as often as possible. Patches are initiated on supported gadgets all around the globe by Apple. Customers who update their systems fast enjoy fast security patches, reducing the risk of falling prey to familiar attacks.
Biometric Protection

Touch ID and Face ID aid in convenient authentication. These applications save the biometric data in the device as it is encrypted instead of storing it in external servers. This will reduce the probability of massive biometric data breaches.
Privacy-Focused Features
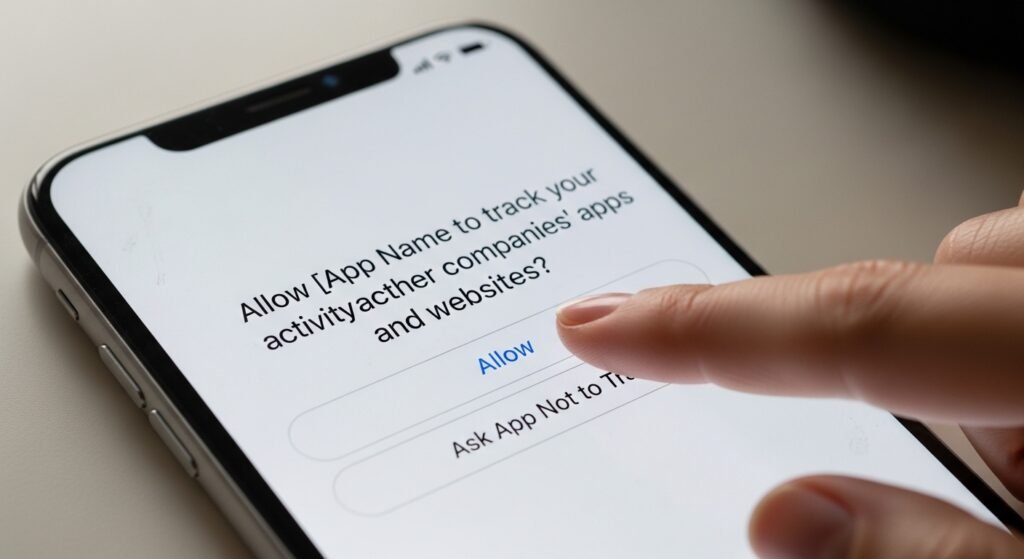
Features like App Tracking Transparency provide more control over the sharing of data. Background tracking is not allowed without permission on Apple. These restrictions enhance privacy but they cannot eliminate all possible third-party data gathering threats.
Phishing and Social Engineering Risks
Even robust systems do not help users not to give in to the misleading links. Phishing email messages and fraud texts are directed at individuals. Insecurity or insecurity lies not only in the architecture of a device but also in awareness.
Zero-Day Vulnerabilities

There is no platform that cannot have undiscovered deficiencies. At times, researchers discover zero-day exploits to iOS or macOS. The exposure can be created through these few seconds, though Apple is normally fast, responsive.
Cloud Security Considerations

Such things as iCloud are added to the services such as an encrypted backup. Cloud accounts, however, are still the victims of credential theft. The reuse of a credential or having weak passwords can be used to compromise good device-level protection.
Third-Party Application Risks

Some malicious apps cannot be detected despite being reviewed. Advanced malware may seem to be valid on the surface. Weaknesses in third-party software can also allow it to develop entry points that are not directly under the control of Apple.
Device Theft and Physical Access

When a device gets into the wrong hands, there may be physical access attempts. Good passwords and automatic lock systems are also necessary. Protections on hardware are helpful but configuration by the user is important.
